Search results for tag #infosec
Why people working on software where something serious is at stake would throw out known gradient to use a code generator + testing is beyond my capacity to understand.
https://1password.social/@1password/116580082041363054
#AI #GenAI #GenerativeAI #LLM #VibeCoding #Software #SoftwareDevelopment #tech #dev #security #InfoSec #PasswordManagers
the last weeks we saw more and more security issues coming up. Let's talk!
Sorry, a pretty long blog post about this...
https://gyptazy.com/blog/coding-after-ai-are-humans-still-good-enough/
#ai #aicoding #coding #opensource #foss #security #infosec #vulns #developer #devops #engineer #ops #fedi #philosophy
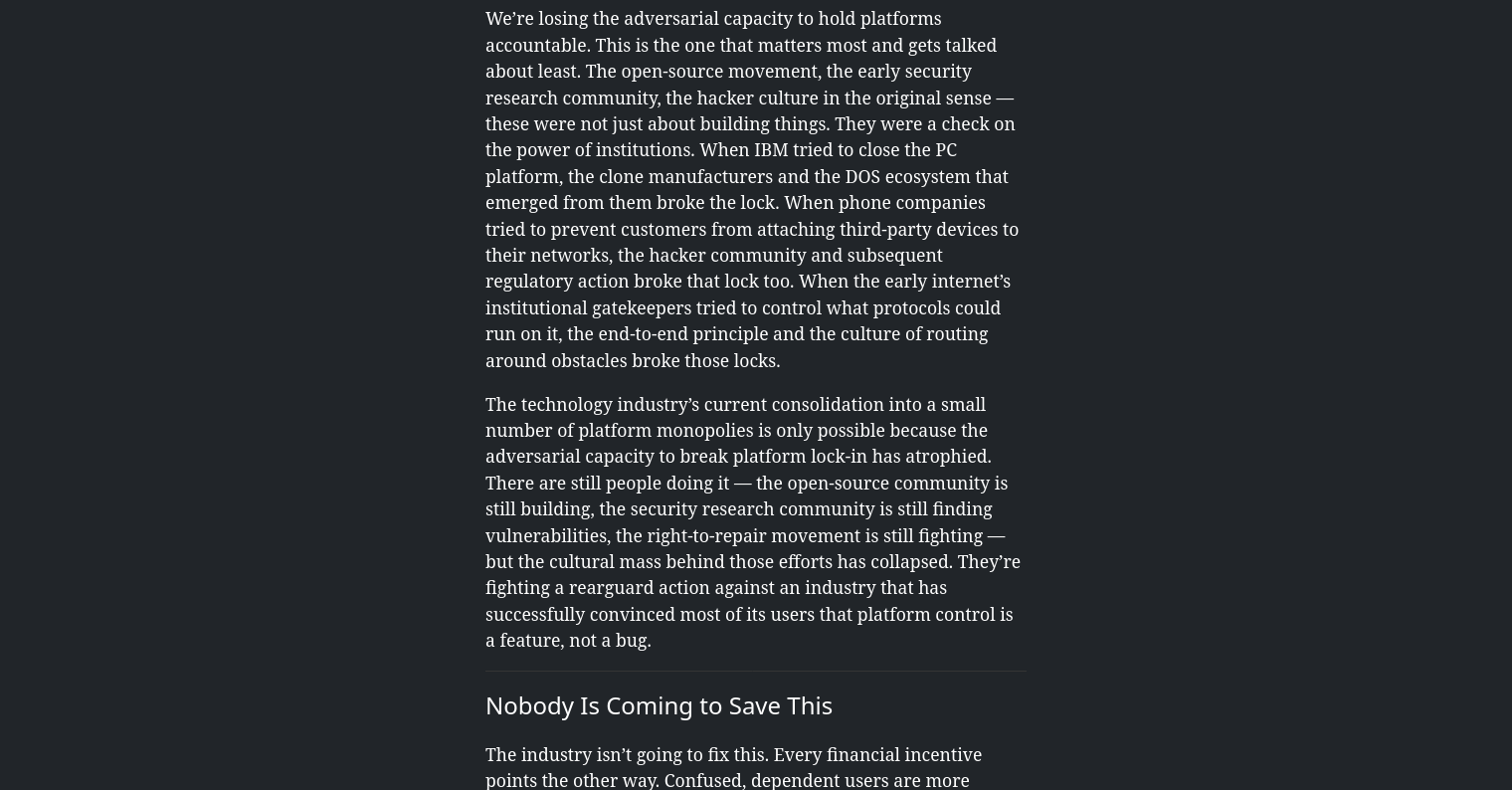
Reading this blow post makes you angry at vendor & platform lock in
Do something about it
# FIGHT
Athropy is used here
https://fireborn.mataroa.blog/blog/the-slow-death-of-the-power-user/
#Slow #Death #Power #User #OpenSource# #programming #InfoSec #Closed #Source #meta #aplhabet #FB #enshittification
About that... We now have a fourth vulnerability: ssh-keysign-pwn. Despite the first three letters, this is a Linux kernel vuln. PoC already available.
The more you read this piece of excellent work the more you realize how much energy we, as the Open Source community, the programma's and the users, shall need to put in another to get a proper Balance Again
Read the section here.
Source:
https://fireborn.mataroa.blog/blog/the-slow-death-of-the-power-user/
#Power #User #Walled #Garden #programming #InfoSec #privilege #feature #parameters #control #OpenSource against #Meta #FB #Alphabet #Enshittification #Google #Elon #Musk #Twitter #Facebook #WTF
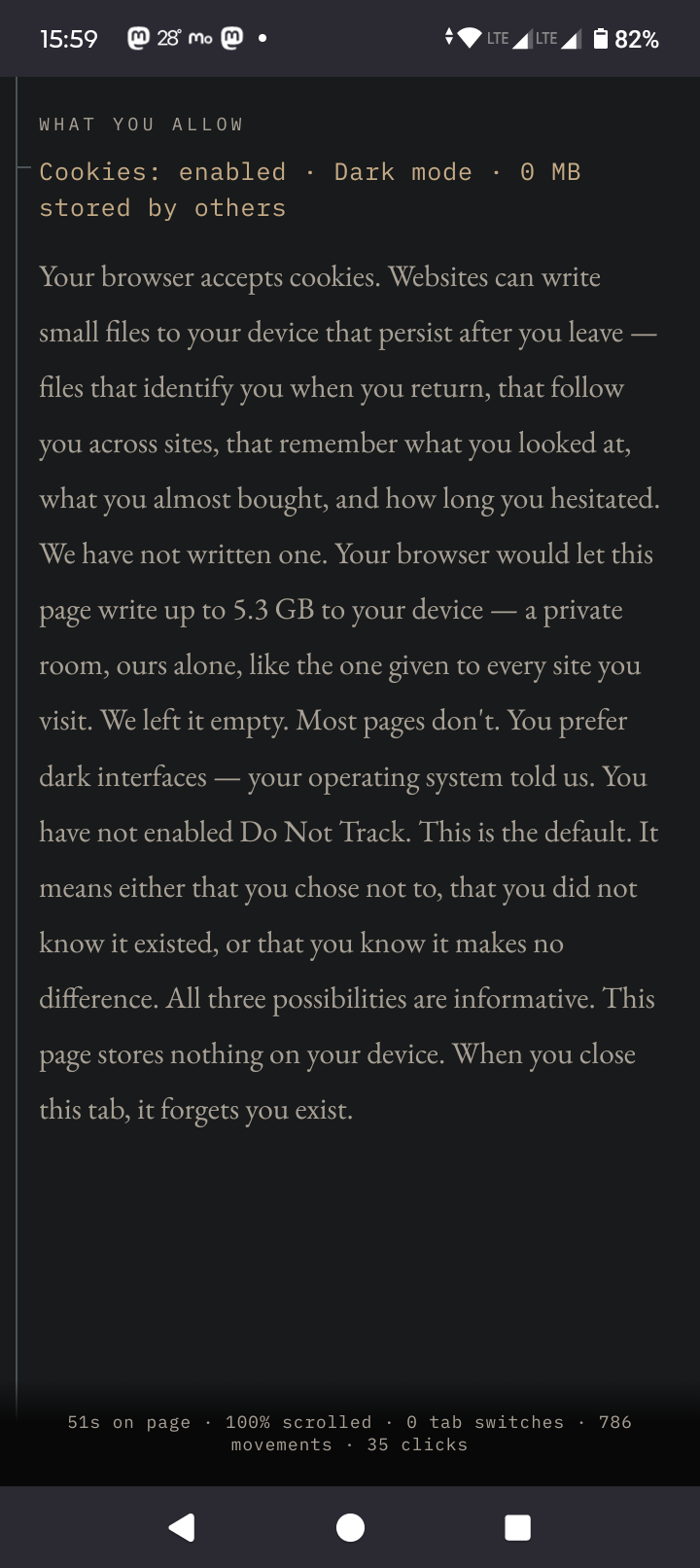
I knew my browser was chatty but I didn't know that my browser on Android was so chatty and so wonderful with giving out free space
Space that I need!
Sources
🧵 Pixel art works, 8/x
Isometric pixel illustration for a Dutch infosec company.
#PixelArt #InfoSec #security #privacy #safety #data #CharacterDesign #graphics #design #artwork #2D #vector #illustration #illustrator #fantasy #picture #DigitalArt #OriginalArt #digital #experimental #style #art #artist #arts #arte #designer #GraphicDesign #minimalism #NoAI #HumanArt #ArtLovers #FineArt #painting #drawing #doodle #sketch #MastoArt #FediArt #MastodonArt #CreativeToots #ArtistsOnMastodon
RE: https://cyberplace.social/@GossiTheDog/116565662607962457
This YellowKey Bitlocker Bypass Vulnerability is seriously crazy. As if someone found a government / law enforcement backdoor.... #infosec #cybersecuity
So I’ve just had a quick play with this and yes, it works. Essentially BitLocker has a backdoor. https://github.com/Nightmare-Eclipse/YellowKey
Mitigation = BitLocker PIN and BIOS password lock.
@stefano Hear, hear. And in n years the ability of bad or indifferent actors to collate data will be fantastically better. Not sure if it helps but I made a throwaway email address with a provider that had an email app of its own, so I could chat to estate agents without risking ++ spam. It was so useful that I kept it. In retrospect, I should have added a second pay as you go sim card. I'd wager that thoughtful clubs might let one use a nickname or non de plume and pay with cash or cryptocurrency. I'm guessing if all this was an option you'd have suggested it, but I thought it worth mentioning in this thread for completeness' sake.
#infosec #countersurvillance #privacy #personalData #security
Hardened OSs like #GrapheneOS do a great job, but we have a major blind spot: The Hardware.
Modern phones are networks of dozens of "black box" computers (UFS, Baseband, Wi-Fi) running proprietary code we can't audit, disable, secure or replace.
Why this matters:
1️⃣ Persistence: Malware in your UFS/SSD controller survives a factory reset.
2️⃣ Tracking: Hardware Attestation acts as an immutable digital fingerprint.
3️⃣ Shadow Attacks: Zero-click exploits hit your Wi-Fi or Baseband before the OS can even react.
We are calling for #HardwareSovereignty. Inspired by the #OpenBSD philosophy, we demand:
✅ Open & replaceable firmware for ALL subsystems.
✅ User-controlled hardware toggles.
✅ Trust minimization that includes the manufacturer.
It's time to move from "Vendor-Enforced Security" to User Sovereignty.
Read the full Open Letter here: https://pastebin.com/RzRbzhwn
#HardwareSovereignty #Infosec #CyberSecurity #Privacy #OpenSource #TechFreedom
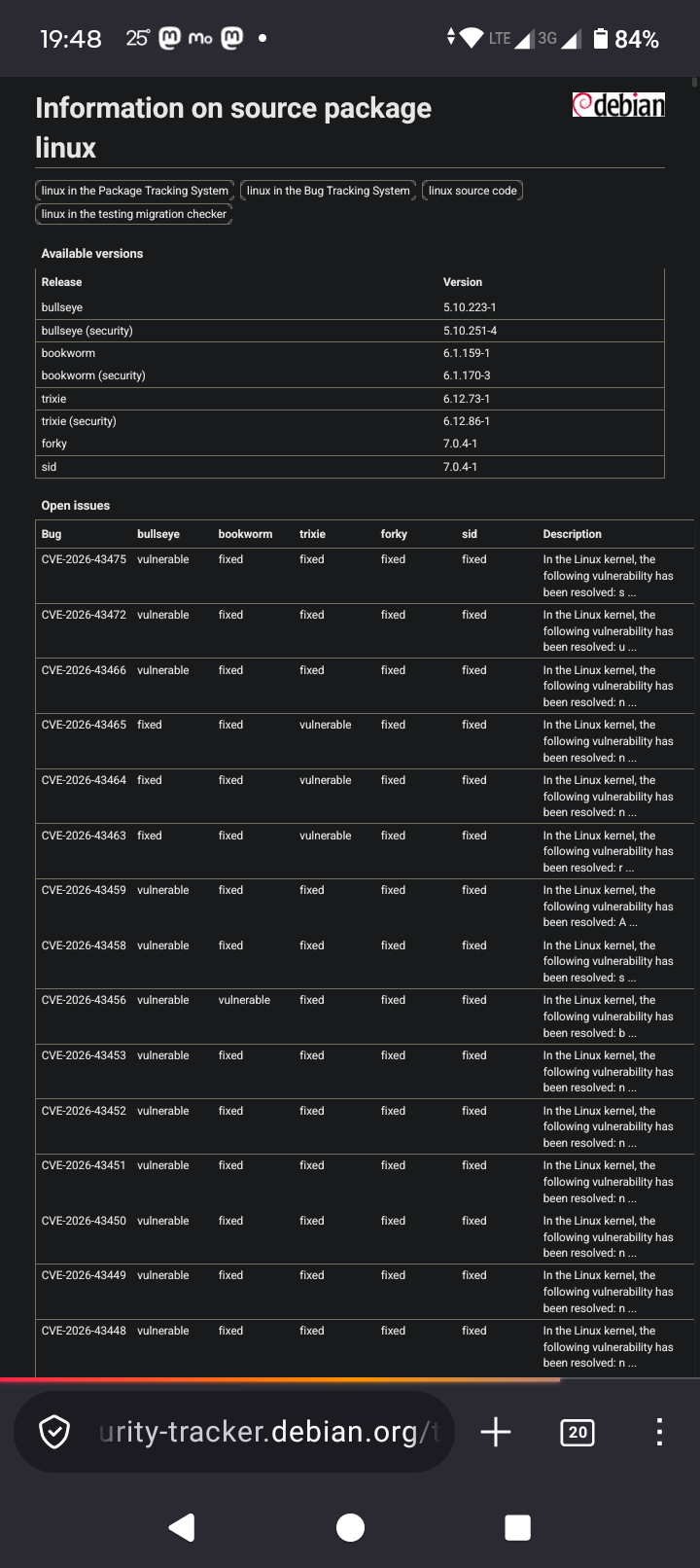
Patch your Linux home and production servers / clients
Privilege escalation bug
Instead of asking yourself why the second bug🥈 in 2 weeks has been found on such a level, be glad that it has been found
Just patch and move on
Note
These bugs only occur local not over the network over the internet.
Local_privilege_escalation
Sources
https://lists.debian.org/debian-security-announce/2026/msg00169.html
https://security-tracker.debian.org/tracker/source-package/linux
#InfoSec #programming #privilege #escalation #root #Linux #All #distributions #severe #high
Moscow shutting down internet in May 5th to May 9th in order to ensure Victory Day parade security.
What I want to highlight is, if it is started by one country, the other will follows.
First, they banned VPNs, now the west also trying to ban VPNs.
What is gonna be next? Digital firewall?
I am here just telling we need to prepare and prevent your country to fall into this oblivion of internet freedom.
https://militarnyi.com/en/news/moscow-to-shut-down-mobile-internet-on-may-9-for-parade-security/
Everybody hates #robocalls. But, despite tech reporting being willing to give the #FCC leeway, this new measure is not to stop robocalls, it won’t do a damn thing to stop robocalls. What it does is make burner phones illegal.
Burners are an integral part of many social justice actions. Protestors use them to record #ICE and other #cops. We include them in “Go Bags” to let abused women and children escape. They allow for anonymity.
They are a thorn in the side of the panopticon, and they are moving to eliminate them.
Stock up kids.
https://mashable.com/article/fcc-proposes-to-battle-spam-calls-at-the-expense-of-privacy-protections
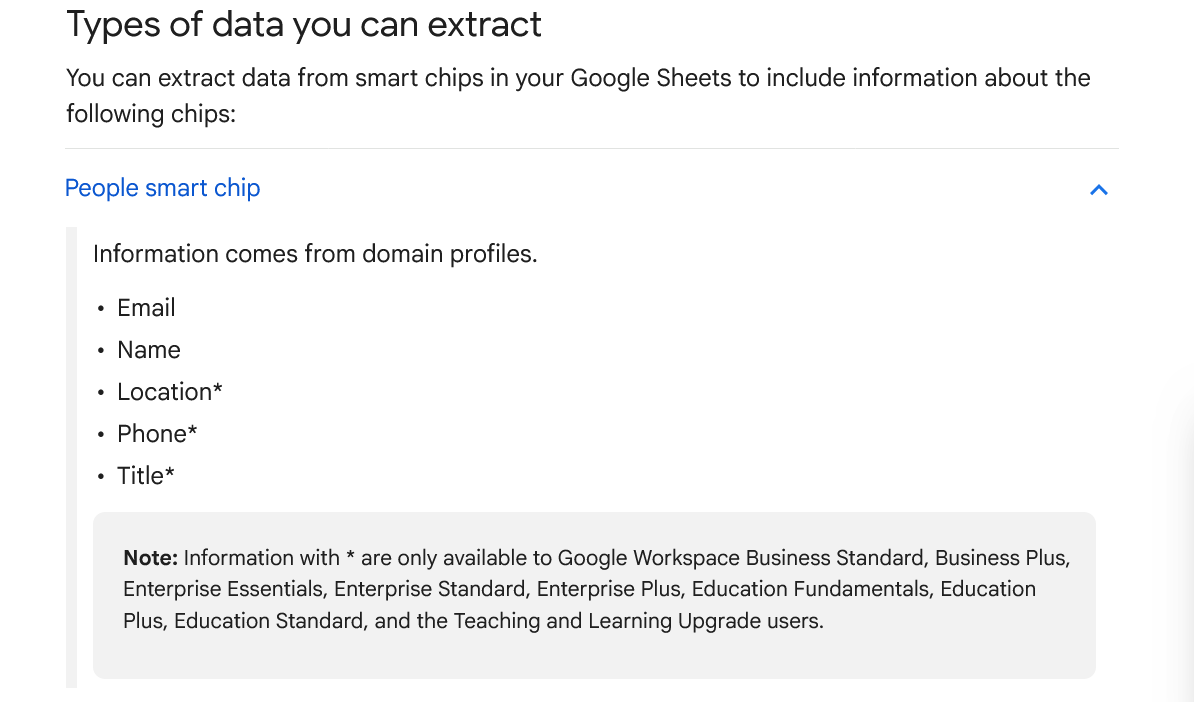
New Google Sheets "Chip" feature lets you extract data about people.
My takeaway: if you view a shared Google Sheet while logged into a Google Account, the doc owner (maybe others) can extract your location & phone. 1/n
https://support.google.com/docs/answer/13524011#zippy=%2Cpeople-smart-chip


 [
[